Product Security
At bioMérieux, we are committed to the security of our instrumentation and solutions as well as the protection of the data that they process. bioMérieux recognizes that an effective cybersecurity program must address the entire product lifecycle including training, requirements, design, implementation, verification, release, risk assessment, vulnerability management, response, and disposal of a product and any associated data. bioMérieux integrates cybersecurity and data privacy measures early on in product design, conception, manufacture, assessment, testing, and validation phases. bioMérieux products are designed to follow privacy and security standards such as HIPAA, HITECH, 21CFR part11 CLSI (AUTO11-A2), ISO, ANSSI, and recent GDPR, as well as FDA, ANSM, and NMPA clinical regulations and industrial integrity standards.
As the security threat to healthcare facilities and instrumentation evolves so does our commitment to ensure our products and systems maintain high-security standards to meet our customer's information security needs.
Products
MYLA Lab Analytics is an add-on data visualization module that integrates advanced business intelligence with the standard statistical reporting module of MYLA. Users who opt to purchase the license for MYLA Lab Analytics will experience the benefits of customizable reports, data querying, and drill-down capabilities. This platform retrieves the required data from MYLA, with synchronization occuring every day. With the standard license option of MYLA Lab Analytics, users can navigate through existing dashboards and export stories or data for further communication to stakeholders. With an advanced license, users can duplicate existing dashboards as well as create unique, customized sheets.
CLARION is a secure, cloud-based clinical informatics software-as-a-service that connects and integrates disparate data into a single management application. CLARION gives you a holistic view of relevant lab and clinical data across departments, processes, and vendors and translates this data into actionable insights visualized on easy-to-use dashboards.
Utilization of our intuitive CLARION platform provides the capability to track and improve metrics that can impact patient care and outcomes. We leverage our expertise in microbiology and infectious diseases to help health systems understand their current processes then visualize and analyze their data.
VILINK is a highly-secured modular solution that is firewall-configurable and compatible with your organization’s security systems. VILINK provides a direct connection between bioMérieux’s technical support representative and bioMérieux systems hosted within your facility. It features full traceability and data security via user-approved access and TLS-based encrypted communication. VILINK enables our service support teams to offer real-time troubleshooting and operator training at your request, reducing downtime and improving efficiency in your laboratory.
VILINK’s patented Firewall-Friendly™ technology provides two-way, in-session communication based on Web Service standards, including Hypertext Transfer Protocol (HTTP), Simple Object Access Protocol (SOAP), and Extensible Markup Language (XML). All outbound communications are initiated using the HTTPS protocol exclusively on port 443 outbound.
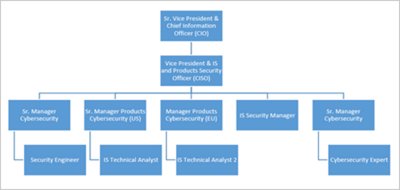
Services/Teams:
- IT Security Team
- Service Offerings: bioMérieux offers a variety of services that can support your organization security needs. Please visit Service Agreement Options page for additional details about how we can help.
FAQ:
A: Our customer's IT department or laboratory personnel are responsible for any and all updates of Microsoft Windows OS Security patches as well as updates to any and all anti-virus/anti-malware solutions installed on bioMerieux provided PCs. bioMérieux will update the device applications with all necessary patches by means of periodic software/firmware updates, as needed.
A: bioMerieux does not create, transmit, or store customer data. All customer data remains on-site at the customer's facility and/or data center. bioMérieux will never remove customer data from instrumentation without first obtaining prior, written consent from the customer. Data is only removed from customer network and/or device in cases of troubleshooting and investigation.
When instrument data is needed for troubleshooting and/or investigation bioMérieux service representatives will send the customer a secure Coltshare link for remote data transfer or come on-site to export the instrument data via a cipher encrypted USB drive.
A:
- Product Documentation: bioMérieux security contact can share product documentation such as the Manufacturer Disclosure Statement for Medical Device Security (MDS2), Security White Papers, & Software Bill of Materials (SBoM) upon request.
- Security Policies and Procedures: At this time bioMerieux cannot release internal policies and procedures as they are considered highly confidential. In order to protect the integrity of our systems and ensure the highest level of security is maintained for all of our customer’s information, they cannot be shared outside of the organization. Currently, all we can offer is for the documents/policies to be viewed on-site at bioMerieux under observation. Please reach out to the bioMérieux security contact for more information.
A: Tenable.IO scans occur weekly on internal systems, and results are handled in accordance with the Post Market Cybersecurity Patch Management Program. Raw Tenable.IO results are confidential and cannot be shared outside of the organization, however customers are notified of the results of the Product Patch Management Program.
Tenable.IO scans are performed by consultants using internal resources and working with employees to evaluate results.
Real-time monitoring performed using CERT-IST (THALES Group)
Product vulnerability scans and penetration tests are performed on the bioMérieux products on bioMérieux sites. Results are used to prepare security communications and create security patches, if necessary.
A: bioMérieux uses an active directory along with bioAccess identity management (SailPoint IIQ) to grant, suspend, and delete user accounts. This automated process is linked to each user in the enterprise and accounts are immediately disabled upon separation from the company. Additionally, an internal audit is performed by the AD team every 30 days to ensure accounts are active and roles are accurate to the job description of the employee to which they are assigned with the principle of least privilege in consideration.
Compliance Regulatory:
Microsoft Security Response Center
https://msrc.microsoft.com/update-guide/
Cybersecurity & Infrastructure Security Agency
CERT Coordination Center
U.S. Department of Health & Human Services - Health Information Privacy (HIPAA)
Security Contact:
Chris Boyd
Project Manager, IT Security
bioMérieux Inc.
Christopher.Boyd@bioMerieux.com(link sends e-mail)
PRN 060442 Rev01.A